As pointed out in my previous post, I was looking into flashing the D-Link DBT-120 USB bluetooth adapter with Apple’s Bluetooth Firmware update so it becomes HID proxy-capable.

Now I do not have any machine running MacOS X, so I could not simply download and run Apple’s tool and was therefore looking into alternatives, aiming at extracting the firmware from Apple’s download somehow and using other means to flash the firmware. And obviously I wasn’t the only one.
Extracting the firmware
After downloading from Apple you’ll have a file BluetoothFWUpdate1.2.dmg. .dmg files are basically Apple Disk images, representing so-called volumes. In the simplest case running Linux’s file utility on such a .dmg would give you an output such as:
$ file example.dmg
example.dmg: Macintosh HFS Extended version 4 data last mounted by: ’10.0′, created: Fri Jan 30 11:12:33 2009, last modified: Fri Jan 23 12:09:55 2009, last checked: Fri Feb 07 04:22:58 2009, block size: 4096, number of blocks: 6400, free blocks: 218
In such a case you would be able to mount it with a command such as modprobe hfsplus; mount -t hfsplus -o loop example.dmg /mnt.
In our case, however, things are a bit more complicated:
$ file BluetoothFWUpdate1.2.dmg
BluetoothFWUpdate1.2.dmg: VAX COFF executable
file gets a bit confused here: in reality this is a compressed .dmg file that requires a conversion with the dmg2img utility. Download it, make sure you have zlib and bzip2 development headers installed and run make to compile it. Then, run it like this:
$ dmg2img-1.6.5/dmg2img BluetoothFWUpdate1.2.dmg
dmg2img v1.6.5 (c) vu1tur (to@vu1tur.eu.org)
BluetoothFWUpdate1.2.dmg --> BluetoothFWUpdate1.2.img
decompressing:
opening partition 0 ... 100.00% ok
opening partition 1 ... 100.00% ok
opening partition 2 ... 100.00% ok
opening partition 3 ... 100.00% ok
opening partition 4 ... 100.00% ok
Archive successfully decompressed as BluetoothFWUpdate1.2.img
Now we have a 1:1 image of a HFS+ filesystem (the filesystem Apple uses) and can mount it:
$ sudo mount -t hfsplus -o loop BluetoothFWUpdate1.2.img /mnt
If we now examine the mounted image’s contents, we’ll find a lot of MacOS X packaging-related files and a file Archive.pax.gz that we care about:
$ cp /mnt/BluetoothFirmwareUpdate1.2.pkg/Contents/Archive.pax.gz .
$ umount /mnt
This file is obviously gzip-compressed, so let’s uncompress and examine it:
$ gunzip Archive.pax.gz
$ file Archive.pax
Archive.pax: ASCII cpio archive (pre-SVR4 or odc)
cpio archives are something we know a bit about in the Unix world, so let’s create a subdirectory to extract its contents:
$ mkdir unpack
$ cd unpack
$ cpio -if < ../Archive.pax
5390 blocks
We'll now again have a quite verbose, MacOS-typical directory structure. Dive deeper and you'll find what we're looking for:
$ cd Applications/Utilities/Bluetooth\ Firmware\ Updater.app/Contents/Resources/
$ ls
total 2324
drwxrwxr-x 17 pief users 4096 Feb 21 21:12 .
drwxrwxr-x 4 pief users 4096 Feb 21 21:12 ..
-rwxrwxr-x 1 pief users 638672 Feb 21 21:12 DeskTop.dfu
drwxrwxr-x 3 pief users 4096 Feb 21 21:12 Dutch.lproj
drwxrwxr-x 3 pief users 4096 Feb 21 21:12 English.lproj
-rw-rw-r-- 1 pief users 34690 Feb 21 21:12 FirmwareDownload.icns
drwxrwxr-x 3 pief users 4096 Feb 21 21:12 French.lproj
-rwxrwxr-x 1 pief users 994866 Feb 21 21:12 GenericCSR.dfu
drwxrwxr-x 3 pief users 4096 Feb 21 21:12 German.lproj
drwxrwxr-x 3 pief users 4096 Feb 21 21:12 Italian.lproj
drwxrwxr-x 3 pief users 4096 Feb 21 21:12 Japanese.lproj
-rwxrwxr-x 1 pief users 638672 Feb 21 21:12 Portable.dfu
drwxrwxr-x 3 pief users 4096 Feb 21 21:12 Spanish.lproj
drwxrwxr-x 3 pief users 4096 Feb 21 21:12 da.lproj
[...]
Those .dfu files are what we were looking for, because of their file sizes and, in the case of GenericCSR.dfu, also because of its file name. Remember, we’re going to flash a CSR-based device.
Now it looks like we have three files to choose from: DeskTop.dfu, GenericCSR.dfu and Portable.dfu. “Generic” does suggest to be a good choice as “DeskTop” and “Portable” sound like firmware update files for special cases, but we wouldn’t take a bet on that. Running strings on each of them does not shed light into the darkness, however. But worry not, we’ll see more in a minute once we feed the files to the flash utility.
Flashing the firmware
In general there are two ways to backup and update the firmware of CSR-based USB bluetooth adapters:
- under Linux with the BlueZ project‘s dfutool.
- under Windows with a software suite from CSR themselves called “BlueSuite”.
I played around with Linux at first, examining the D-Link DBT-120’s properties before the flash upgrade with commands such as lsusb, hciconfig hci0 version and hciconfig hci0 revision. bccmd chiprev and bccmd buildname gave me an error message about an “Unsupported manufacturer”. But, more importantly, dfutool worked and I could get a backup of the existing firmware with dfutool archive dlink-dbt120.dfu.
However, I still wasn’t sure which of the three Apple .dfu files to flash. So I looked around on the Internet for CSR’s BlueSuite software for Windows. I checked their Website and found the CSR Developer Zone. To my surprise, they would let me get myself registered without any barriers, payments or anything. I ignored the warning about the “unknown mail domain” that would cause me “not to have full access” for the moment and was pleasantly surprised to find a BlueSuite 2.5.8 download (plus a user guide) on the “Last updated” page. Nice work, CSR, that’s how things should be! :)
BlueSuite is a collection of different development-related tools, some graphical, some command line-based:
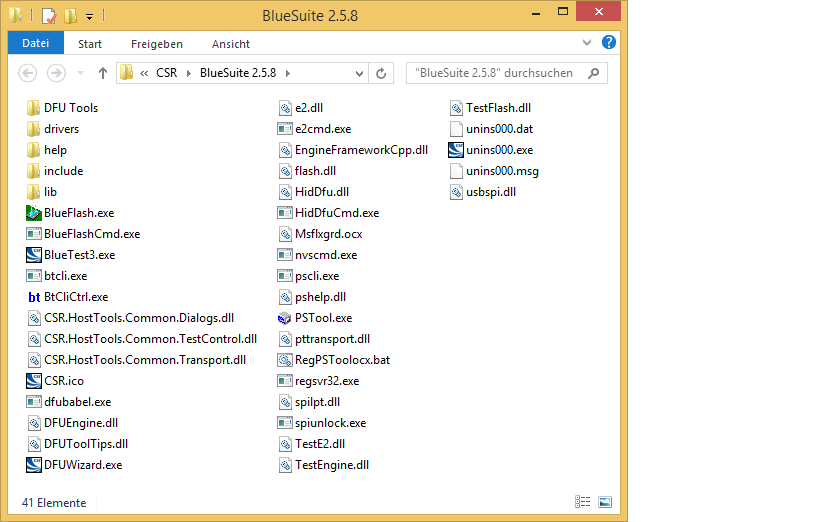
It also comes with a special driver for accessing the Bluetooth adapter. Prior to installing that driver, if you look at Windows’ device manager and use Microsoft’s built-in Bluetooth stack (ie. not Widcomm, BlueSoleil, CSR Harmony etc.) you should see a “Generic Bluetooth Radio” device in the “Blutooth” category (screenshots from a German Windows version):
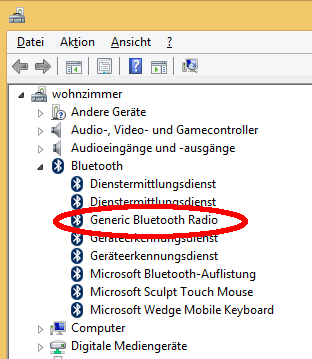
You should also have a blue Bluetooth icon in the task bar’s notification area.
After installing the BlueSuite’s driver by running drivers\win64\DPInst.exe the Bluetooth icon will disappear and Windows’ device manager will now list an entry “CSR BlueCore Bluetooth” in the “USB controllers” category:
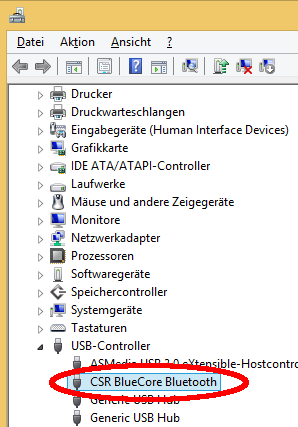
This is a prerequisite in order to be able to use the BlueSuite utilities including our flashing tool DFUWizard.exe:

Choose “USB” as connection method and select one of the three .dfu files we extracted earlier. You’ll notice that DFUWizard shows human-readable descriptions that are more useful than dfutool‘s:
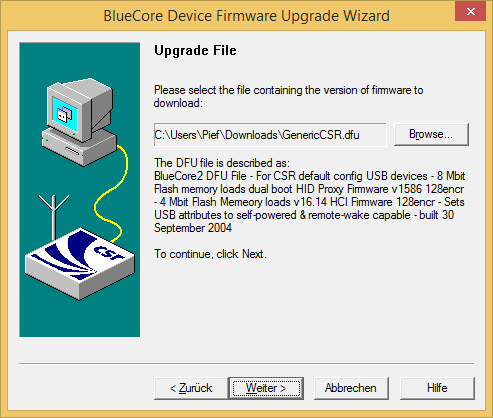
GenericCSR.dfu looks to be the right candidate. So we’ll use it for flashing.
WARNING1: Flashing can render your device unusable, eg. if power outages occur or the wrong file is flashed. Do not perform the flashing process unless you know what you’re doing! I can not help you if something goes wrong!
WARNING2: Flashing Apple’s firmware will render your DBT-120 unless you’ve taken care of obtaining hid2hci.exe! Do not ask me for this tool.
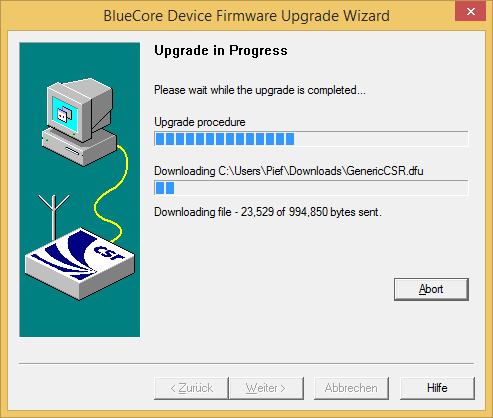
This process should take just a minute and if things go right you should get a result such as this:
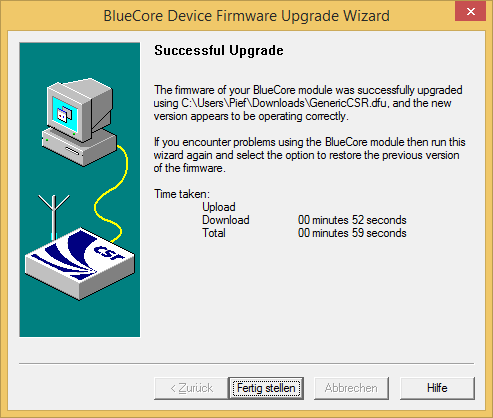
Congratulations, you now have a DBT-120 adapter that behaves as a HID proxy. You should now try running hid2hci.exe and pair your input devices again. After a reboot, they should work in the BIOS as well. Remember that returning to Windows you will need to run hid2hci.exe again to get them working. A followup post will deal with automation of this.
Thank you so much for this post!
It describes precisely the solution I was looking for in order to use my DBT-120 for keyboard input before and after MS Windows starts.
Do I need to run hid2hci.exe each time Windows starts even if I use the DBT-120 with modified firmware for keyboard input only? Or is hid2hci.exe merely needed to enable other BT services under Windows?
I am asking because (if possible) I would prefer to stick with the HID proxy way of transmitting keyboard input, even after Windows is started.
The latter. Running hid2hci.exe will, as the name says, switch the dongle from HID mode to HCI mode. In HCI mode you need a full Bluetooth driver stack, such as the one that comes with Windows, but you will be able to eg. pair other devices.
If you don’t need that, just try it out whether NOT running hid2hci.exe and leaving the DBT-120 in HID mode works for you.
Looks like downloading the firmware loading tool is now limited to customers .
Your email domain is not on our customer email list. This may mean you will not have access to all the documents you require and may lead to your requests for further access to be denied. Please contact your local CSR sales representative to rectify this http://www.csr.com/contact/sales-representatives . If you still wish to use this email address please click ‘register account’ once again.